DOLPHIN X RAT Technical Deep-Dive, TTPs, Detection Controls & AI-Driven Defense
BLUF — Bottom Line Up Front
What it is: “Dolphin X RAT” is a Malware-as-a-Service (MaaS) toolkit advertised on May 10, 2026 by threat actor “Kontraktnik” on BreachForums, HackForums, and Cracked. The actor claims 212 features across 9 capability categories.
Threat level: Moderate-to-High, pending independent validation. The advertised feature set — HVNC, credential theft, metamorphic evasion, crypto clipping, and bootkit-level persistence — reflects mature, well-understood techniques seen across other commodity malware families. No independent sandbox analysis or live samples have been confirmed at time of publication.
Key defensive priorities:
1.Deploy EDR with behavioral (not signature) detection, especially hidden-desktop (DesktopName/CreateDesktop) rules.
2.Enable UEFI Secure Boot plus VBS/HVCI to raise the bootkit bar.
3.Enforce universal MFA to neutralize credential theft as a lateral movement enabler.
4.Deploy ML-based NDR to detect HVNC reverse-channel C2 beaconing.
5.Integrate AI triage/hunting agents to manage detection alert volume at scale.
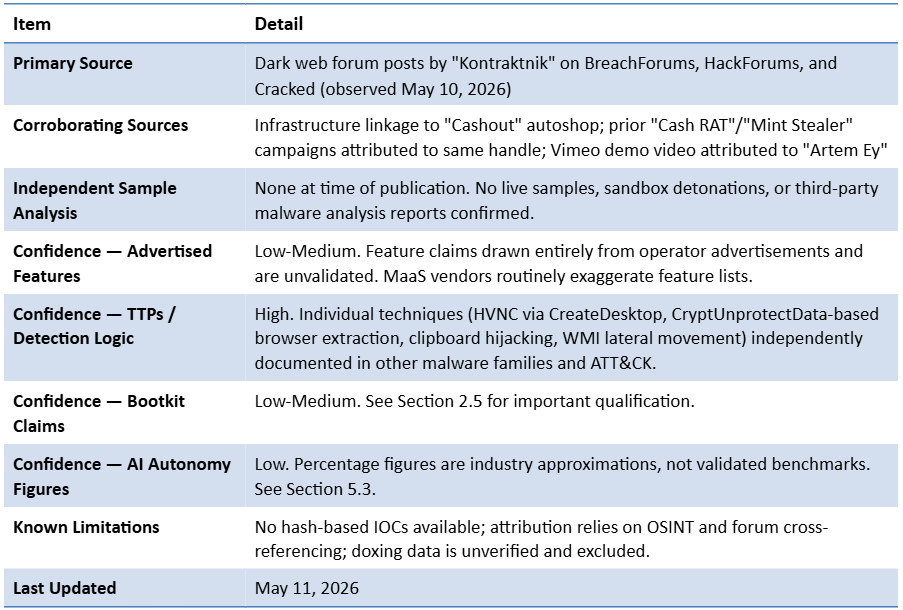
Sources, Confidence & Limitations
Executive Summary
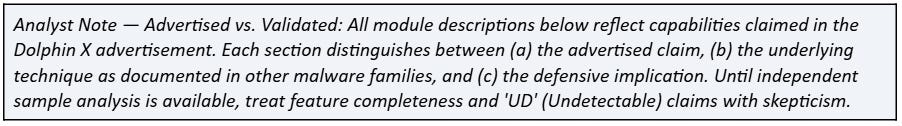
On May 10, 2026, a threat actor operating under the handle “Kontraktnik” advertised a new all-in-one malware toolkit called “Dolphin X RAT” across multiple dark web forums including BreachForums, HackForums, and Cracked. The actor claims 212 features across 9 capability categories. All feature descriptions in this report reflect advertised capabilities; independent sample validation has not been completed at time of publication.
The advertised toolkit purportedly integrates Remote Access Trojan (RAT) functionality, a credential stealer, Hidden Virtual Network Computing (HVNC), a crypto clipper, DDoS capabilities, bootkit-level persistence, metamorphic code obfuscation, and lateral movement tooling — all wrapped in a subscription model starting at 69.95 euros per month.
The actor self-identified as a Russian national and malware developer, and has cross-promoted the tool under the same handle on multiple forums, linking to a shared infrastructure (”Cashout” autoshop) that has historically distributed other malicious products. This convergence of indicators is consistent with a seasoned threat actor, though definitive attribution requires further corroboration.
This report provides a technical breakdown of the advertised functional modules, maps them to the MITRE ATT&CK framework, outlines concrete detection and mitigation controls, and explores how modern AI agents can be deployed to combat this class of threat.
1. The MaaS Model & Threat Context
Dolphin X follows the increasingly professionalized Malware-as-a-Service (MaaS) business model — a paradigm where malware developers monetize their tools via subscription tiers rather than one-time sales. This criminal SaaS structure lowers the technical barrier to entry dramatically: any affiliate with a credit card and a Telegram account can deploy enterprise-grade intrusion capabilities.
MaaS ecosystems like this have sustained growth throughout 2025 and into 2026. Security researchers observed a steady increase in dark web listings promoting subscription-based malware services, with Lumma, Acreed, Katana, and Vidar among the most visible families. Dolphin X enters this landscape as a differentiated “all-in-one” offering — the key commercial distinction being that a single subscription purportedly replaces the need to combine separate stealer, RAT, and evasion tools.
The three-tier pricing structure (Basic at 69.95 euros/month, Pro at 134.95 euros/month, Ultimate at 199.95 euros/month) mirrors legitimate SaaS pricing psychology and places the tool within reach of mid-level threat actors. The infrastructure linkage to “Cash RAT” and the “Cashout” autoshop suggests the same development team has been active in the underground market for multiple years, iterating on their tooling.
2. Core Functional Modules: Technical Breakdown
2.1 Remote Control & Execution (HVNC / Remote Shell)
Advertised claim: Full Hidden VNC capability with an isolated hidden desktop session invisible to the victim.
Technique (independently validated in other families): HVNC exploits the Windows CreateDesktop API to spin up a fully independent hidden desktop session running in parallel to the victim’s active session. The DesktopName property of processes attached to the hidden desktop will differ from the default “Default” or “Winlogon” values. This is the primary Behavioral Indicator of Compromise (BIOC) and forms the basis for the KQL/Sigma/SPL detection rules in Appendix A.
The technique operates via a reverse connection model: the HVNC server on the infected machine calls out to the attacker’s C2, converting an inbound firewall block into a benign-looking outbound connection. This was first widely documented in TinyNuke banking malware’s HVNC implementation and has since been commoditized across APT and commodity malware alike.
Key behaviors of HVNC modules include:
•Creation of a child explorer.exe process attached to the hidden desktop — observable in the process tree as an anomalous explorer.exe spawning from another explorer.exe
•Reverse TCP or WebSocket connection to C2 infrastructure
•Independent browser, file, and clipboard access within the hidden session
•Process isolation meaning standard AV UI monitoring tools will not capture activity from the hidden desktop
2.2 Credential Theft (Stealer Module)
Advertised claim: Multi-vector credential harvesting from browsers, password managers, Discord, VPN configs, and cloud session tokens.
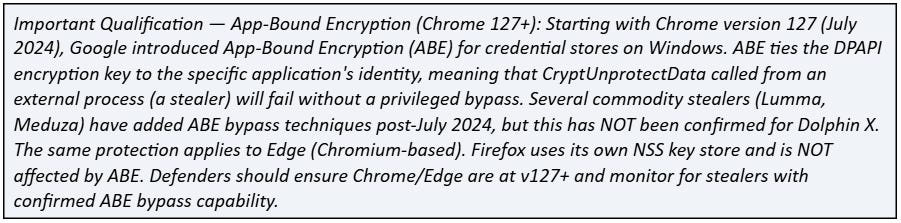
Technique — Browser Credentials (T1555.003): Chrome (and Chromium-derived browsers including Edge, Brave, and Opera) stores encrypted credentials in AppData\Local\Google\Chrome\User Data\Default\Login Data as a SQLite database. The stealer executes a SQL SELECT query against the logins table and decrypts the password field by calling the Windows DPAPI function CryptUnprotectData, using the victim’s cached logon token as the decryption key. No privilege escalation is required for this technique.
Technique — Password Manager Extraction (T1555.005): Password manager extraction targets KeePass (.kdbx file read from disk; in-memory extraction of decrypted credential objects post-unlock), LastPass, 1Password, and Bitwarden. In-memory extraction requires the vault to be unlocked; auto-lock timeouts and process injection mitigations are the primary controls.
Additional credential targets claimed include Discord tokens, VPN configuration files, cloud service session tokens, and browser cookie databases enabling session hijacking without requiring passwords.
2.3 Cryptocurrency Theft (Crypto Clipper + Wallet Extraction)
Advertised claim: Clipboard wallet-address substitution plus direct wallet file and browser-extension extraction.
Technique (T1115): The crypto clipper component monitors the Windows clipboard via the GetClipboardData API. When clipboard content matches a regex pattern for a cryptocurrency wallet address format (Bitcoin, Ethereum, Litecoin, Monero, etc.), it silently replaces the address with an attacker-controlled wallet. The victim copies a wallet address, pastes it, and sends funds — only realizing the substitution after the transaction is irreversible.
Additional advertised wallet extraction capabilities:
•Direct file-system harvesting of wallet.dat files (Bitcoin Core, Electrum)
•Browser extension data extraction targeting MetaMask, Phantom, and other web3 wallets
•Mnemonic/seed phrase interception from clipboard or keylogger context
•Seed phrase injection capability (planting attacker-controlled seeds)
2.4 Monitoring & Surveillance
•Keylogger (T1056.001): Installs a low-level keyboard hook via SetWindowsHookExA, capturing all keystrokes across every active application — including credentials typed directly rather than autofilled.
•Screenshot capture (T1113): Periodically captures or event-triggers full desktop screenshots.
•Webcam access: Advertised: silently connects to the default webcam driver via Windows Multimedia API, captures frames, and uploads. Not independently validated in this sample.
•Microphone recording (T1123): Advertised: uses MCI (Multimedia Command Interface) to record audio and upload silently. Not independently validated in this sample.
•Clipboard monitoring (T1115): Beyond the crypto clipper, continuous clipboard logging captures passwords, OTPs, and sensitive data.
2.5 Stealth, Persistence & Defense Evasion
Metamorphic code rewriting (T1027.005): Metamorphic malware rewrites its entire code base with each generation using functionally equivalent transformations — subroutine reordering, dead-code insertion, register swapping, instruction replacement, and random jump insertion. Every new infection produces a structurally unique binary, rendering hash-based and signature-based detection obsolete. This is an advertised feature; metamorphic capability is technically demanding to implement correctly and quality varies across commodity tools.
Bootkit persistence (T1542.003) — Important Qualification: The advertisement describes bootkit-level UD persistence. This requires careful interpretation:
•True UEFI bootkit: A genuine UEFI bootkit (e.g., BlackLotus, CosmicStrand) embeds code in UEFI firmware or the EFI System Partition, surviving OS reinstallation and disk replacement. It requires a signed UEFI vulnerability exploit (e.g., CVE-2022-21894) and is NOT routine in commodity MaaS offerings.
•What this advertisement likely means: Many MaaS tools advertise ‘bootkit’ capabilities when they actually implement MBR (Master Boot Record) modification. MBR-level bootkits survive OS reinstalls but do NOT achieve UEFI firmware persistence and are detectable and remediable without motherboard reflashing.
•Analyst assessment: Treat the bootkit claim as potentially referring to a less sophisticated variant (MBR or boot sector modification) until a sample is analyzed. Defensive controls should address both scenarios (see Section 4.4).
Windows Defender bypass: Advertised evasion techniques include direct syscalls to ntdll.dll, XOR encryption of shellcode with unique runtime keys, and AMSI patching to disable the Anti-Malware Scan Interface at runtime. “UD” claims from MaaS vendors should be treated as marketing rather than a technical guarantee.
Persistence mechanisms (T1547.001): Standard persistence via Registry Run keys (HKCU\Software\Microsoft\Windows\CurrentVersion\Run), Scheduled Tasks, and startup folder copies.
2.6 Network & Lateral Movement
•SOCKS5 Reverse Proxy (T1090): Tunnels arbitrary network traffic through the compromised endpoint, using the victim’s machine as an egress node or to route C2 traffic through trusted infrastructure.
•AD Enumeration (T1087.002): Advertises use of net.exe, PowerShell Get-ADUser/Get-ADGroupMember, WMI queries, or direct LDAP queries to map the domain: users, groups, computers, trust relationships, and privileged accounts.
•SMB/WMI Lateral Movement (T1021.002 / T1047): Using harvested credentials, moves laterally via SMB Admin Shares and WMI remote execution. Generates Windows Event IDs 4624 (logon) and 4648 (explicit credential use) on target systems.
•DDoS: Volumetric attack capacity using the infected host as a bot node.
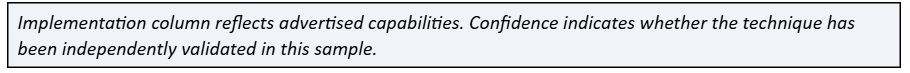
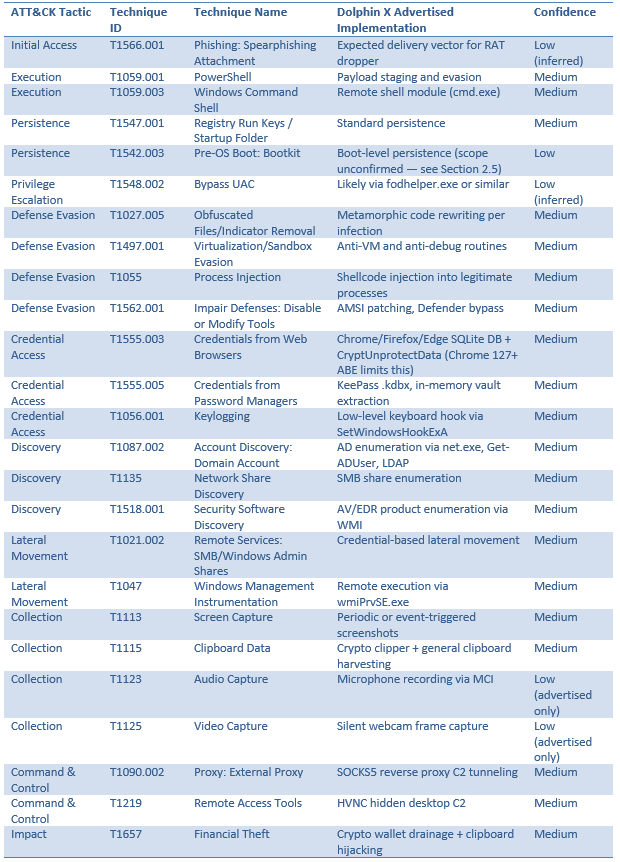
3. MITRE ATT&CK TTP Mapping
4. Technical Detection Controls
4.1 Endpoint Detection (EDR / Sysmon)
HVNC Detection: The core detection signal is an anomalous explorer.exe spawned as a child of another explorer.exe, or any process whose DesktopName property differs from “Default” or “Winlogon”. The DesktopName field is populated from the STARTUPINFO structure at process creation and is visible in EDR telemetry (CrowdStrike, SentinelOne, MDE) and Sysmon Event ID 1 enriched data. See Appendix A for copy-ready KQL, Sigma, and SPL queries.
Key Sysmon rules:
•Event ID 1 (Process Create): Alert on explorer.exe child processes of explorer.exe; alert on processes where DesktopName is not ‘Default’ or ‘Winlogon’
•Event ID 10 (Process Access): Monitor for cross-process memory reads targeting chrome.exe, keepass.exe, 1password.exe
•Event ID 3 (Network Connection): Detect outbound TCP on non-standard ports from explorer.exe or injected processes
Metamorphic malware detection must rely on behavioral indicators:
•Memory execution patterns: VirtualAllocEx + WriteProcessMemory + CreateRemoteThread sequences
•PAGE_EXECUTE_READWRITE allocations at runtime
•Processes without a corresponding disk image (fileless/in-memory execution)
•AI-based behavioral models analyzing instruction sequence entropy and control-flow graph anomalies
Keylogger / Surveillance: Flag processes calling SetWindowsHookExA with WH_KEYBOARD_LL (low-level keyboard hook) outside of known legitimate applications. Similarly flag processes opening MCI audio capture or webcam driver interfaces without user-initiated triggers.
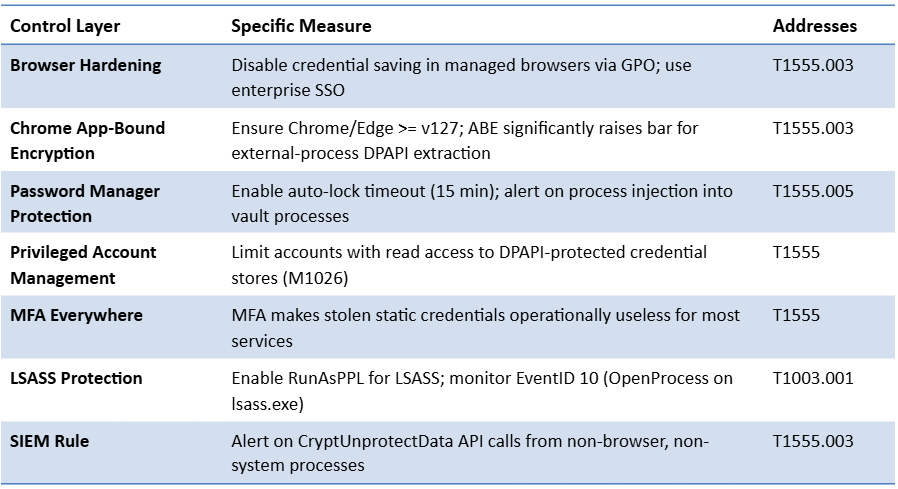
4.2 Credential Theft Prevention & Detection
4.3 Crypto Clipper Mitigation
•Clipboard integrity monitoring: Deploy endpoint agents that hash clipboard content at copy time and re-verify at paste time; any substitution triggers an alert.
•Application allowlisting for clipboard access: Restrict which processes can write to the system clipboard via AppLocker or WDAC policies.
•User training: Verify first and last 5-6 characters of wallet addresses before confirming transactions; use QR codes where possible since clipboard hijackers cannot alter QR-encoded data.
4.4 Bootkit / Pre-OS Persistence Defense
Controls apply regardless of whether the implementation is MBR-level or UEFI firmware-level:
•Enable UEFI Secure Boot and verify proper configuration. If a true UEFI bootkit is confirmed, apply the UEFI revocation list update for CVE-2022-21894.
•UEFI Firmware Scanning: Microsoft Defender Antivirus and Binarly’s platform offer UEFI-level scanning for embedded malicious firmware modules.
•VBS + HVCI: Prevents unsigned kernel drivers from loading, raising the bar for bootkit installation regardless of variant.
•TPM Attestation: Remote attestation detects pre-OS tampering via deviation from known-good boot measurements.
•Monitor for NtLoadDriver calls: Alert on non-Microsoft-signed drivers loaded via NtLoadDriver (BYOVD pattern).
•MBR integrity monitoring: Custom TPM PCR0/PCR4 baseline checks detect MBR modification even without UEFI exploitation.
4.5 Lateral Movement Detection (SIEM / Network)
•EventID 4648: Explicit credential logon events on non-DC hosts from non-service accounts
•EventID 4624 Type 3: Network logon patterns targeting multiple hosts in short time windows
•Sysmon Event 1: Child processes of wmiPrvSE.exe that are not expected system utilities
•Network: Alert on lateral SMB (port 445) connections from workstations to workstations
•AD enumeration: Alert on bursts of ‘net user /domain’, Get-ADUser, or LDAP query sequences from non-DC, non-admin hosts within a time window
4.6 C2 Traffic Detection
•Beacon detection: ML models trained to identify periodic low-and-slow C2 beacon patterns
•Encrypted traffic analysis (ETA): Analyze TLS metadata (certificate age, Subject/SAN anomalies, cipher suites) without decrypting traffic
•Egress behavioral baselines: Flag endpoints establishing outbound connections to new IP/port combinations with no corresponding user-initiated activity
•SOCKS5 proxy traffic: Monitor for SOCKS5 CONNECT requests from non-proxy applications; alert on unusual port forwarding patterns from endpoint processes
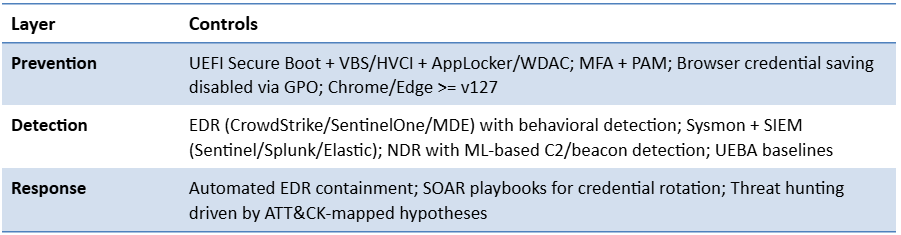
4.7 Defense-in-Depth Architecture
5. Leveraging AI Agents to Combat Dolphin X
5.1 Why Signature-Based Detection Fails Here
Every replication of a metamorphic malware binary produces a structurally unique file while maintaining identical malicious behavior. A signature database built from known samples will miss every new variant. AI-based malware detection addresses this by analyzing behavioral semantics rather than static syntax.
5.2 AI-Powered Detection Capabilities
Behavioral Analysis at Machine Speed: AI-driven endpoint agents build behavioral baselines for every process on every host. When Dolphin X’s HVNC module spawns a hidden explorer.exe, calls CreateDesktop, and establishes a reverse TCP connection, that compound behavioral deviation flags ML anomaly detection models even when each individual action could be explained as benign in isolation.
Metamorphic Malware Detection Techniques:
•Control-flow graph (CFG) analysis: Despite code rewriting, metamorphic malware’s logical execution graph retains structural similarities. ML models trained on CFG features can identify family membership across variants.
•API call sequence modeling: The sequence of Windows API calls (e.g., CreateDesktop -> SetThreadDesktop -> ConnectTCP) is a behavioral fingerprint that survives code mutation.
•Geometric detection: Combines ML with computer vision to identify geometric features in disassembled code that persist across metamorphic generations.
•Sandbox detonation at scale: AI-powered sandboxes classify novel threats via runtime behavioral observation.
5.3 Autonomous AI Agent Architecture for SOC Defense
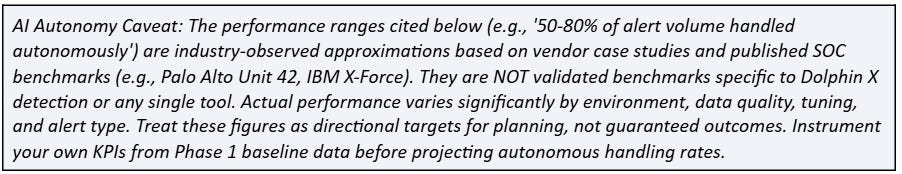
Triage Agent: Receives the raw alert storm and performs initial classification — correlating related events by IP, user, and time window; enriching with AD context, asset criticality, and threat intel feeds; and scoring dynamic risk. Mature deployments have been reported to handle a substantial portion of alert volume autonomously (industry estimates: 50-80% for low-fidelity alert tiers).
Threat Hunting Agent: Proactively hunts for threats using hypothesis-driven workflows mapped to MITRE ATT&CK. Example hypothesis: ‘Is there an HVNC hidden desktop active on any endpoint?’ — the agent searches for explorer.exe processes with a parent of explorer.exe and an active outbound TCP connection, then generates a confirmed or unconfirmed IOC set.
Incident Response Agent: When Dolphin X activity is confirmed, an autonomous IR agent can: isolate the endpoint via EDR API, revoke active session tokens and force password resets, collect forensic artifacts automatically (memory dump, process tree, network connections), generate a kill chain reconstruction, and trigger credential rotation playbooks.
Threat Intelligence Agent: Continuously monitors dark web forums, OSINT sources, and threat intel feeds. For Dolphin X, a TI agent would ingest forum posts, map advertised capabilities to ATT&CK techniques automatically, generate detection rules from the advertised feature list, and feed IOCs into SIEM and firewall block lists.
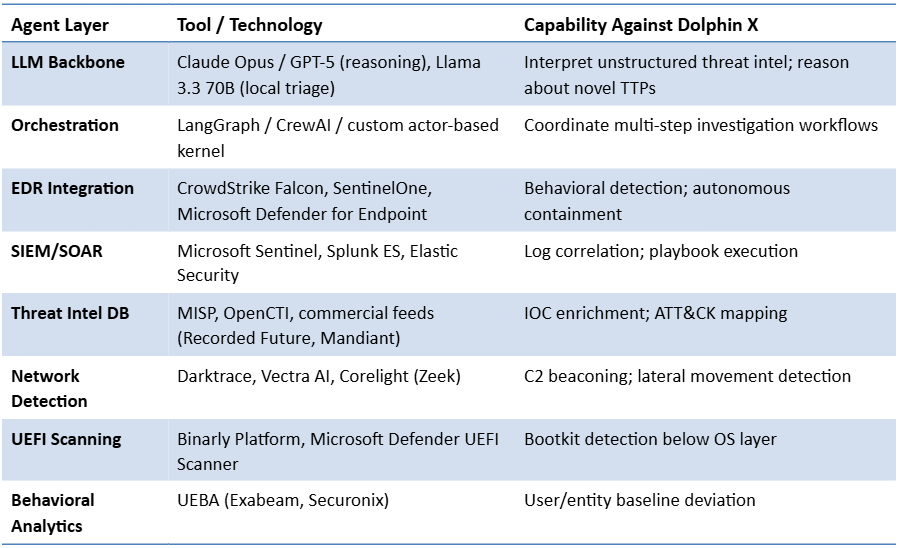
5.4 AI Agent Defensive Stack (2026 Reference Architecture)
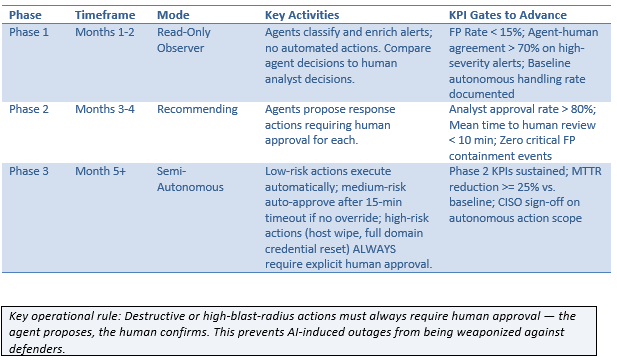
5.5 Deployment Phasing with KPI Gates
AI agent deployment should be phased to prevent over-automation and build analyst trust. Each phase includes KPI gates that must be met before advancing. Do not advance phases solely on time elapsed; gate advancement on KPI achievement.
6. Threat Actor Assessment
The operational consistency of “Kontraktnik” across three dark web forums using the same handle, website, and Telegram IDs is characteristic of a threat actor building brand recognition within criminal ecosystems. The infrastructure linkage to the “Cashout” autoshop — previously associated with “Cash RAT,” “Mint Stealer,” and “Cash Crypter” — suggests either the same individual operating under multiple personas or a small, tight-knit criminal group.
The actor’s self-identification as a Russian national and malware developer, combined with the Vimeo demonstration video attributed to “Artem Ey,” indicates operational confidence in geographic protection from prosecution — a pattern consistent with numerous Eastern European MaaS operators.
7. Behavioral IOCs (BIOCs) to Monitor
Since metamorphic malware renders hash-based IOCs obsolete, defenders should focus on Behavioral IOCs. See Appendix A for copy-ready detection queries implementing these BIOCs.
•explorer.exe spawning a child explorer.exe process
•Any process with a DesktopName property other than ‘Default’ or ‘Winlogon’ (HIGHEST PRIORITY BIOC — see Appendix A)
•Any process with CreateDesktop API calls followed by outbound TCP on non-standard ports
SetWindowsHookExA calls with WH_KEYBOARD_LL hook type from non-allowlisted processes
•CryptUnprotectData calls from processes outside browser processes in the context of the Login Data SQLite path
•MCI audio device opened by non-media application
•Webcam/camera driver access without corresponding user-initiated application launch
•wmiPrvSE.exe spawning cmd.exe or PowerShell on any host
•Clipboard write operations changing data matching cryptocurrency wallet address regex patterns
•Outbound SOCKS5 CONNECT requests from non-proxy processes
•LDAP queries with broad-scope filters (e.g., objectClass=user) from non-DC hosts
•Non-Microsoft-signed drivers loaded via NtLoadDriver
8. Conclusion & Priority Recommendations
Dolphin X RAT represents a significant advertised evolution in the MaaS threat landscape — not because it introduces entirely novel techniques, but because it integrates a breadth of proven attack primitives (HVNC, credential theft, crypto clipping, bootkits, metamorphic evasion) into a single, commercially accessible, subscription-supported toolkit. Defenders should act on the detection controls now; these techniques are active in the commodity threat landscape regardless of this single actor.
Priority recommendations:
6.Deploy EDR with behavioral detection: Focus on hidden desktop detection rules (DesktopName != Default) and memory injection behavioral patterns.
7.Enable UEFI Secure Boot, VBS, and HVCI: Addresses bootkit persistence regardless of whether the implementation is MBR or UEFI level.
8.Implement MFA universally: Credential theft is the primary enabler of lateral movement; MFA neutralizes stolen static credentials.
9.Ensure Chrome/Edge >= v127: App-Bound Encryption meaningfully raises the bar for browser credential extraction.
10.Deploy ML-based NDR: HVNC reverse connections will evade signature-based network detection.
11.Build UEBA baselines: Establish normal behavioral baselines before an incident occurs.
12.Phase AI agents with KPI gates: Do not advance autonomy phases on time alone; gate on false-positive rates and analyst agreement (see Section 5.5).
13.Monitor dark web forums: Monitor infrastructure linked to Dolphin X (Cashout autoshop domains, Telegram handles) for early warning of active campaigns.
The threat is real, technically mature, and actively marketed. Defenders who meet automation with automation — deploying AI-driven defenses calibrated by measurable KPIs — will be best positioned to act on detections before dwell time compounds damage.