CYBER THREAT INTELLIGENCE BRIEFING
Reporting Period: February 10 – March 27, 2026 Runtime: March 27, 2026 Classification: UNCLASSIFIED // OSINT
PART 1: EXECUTIVE SUMMARY
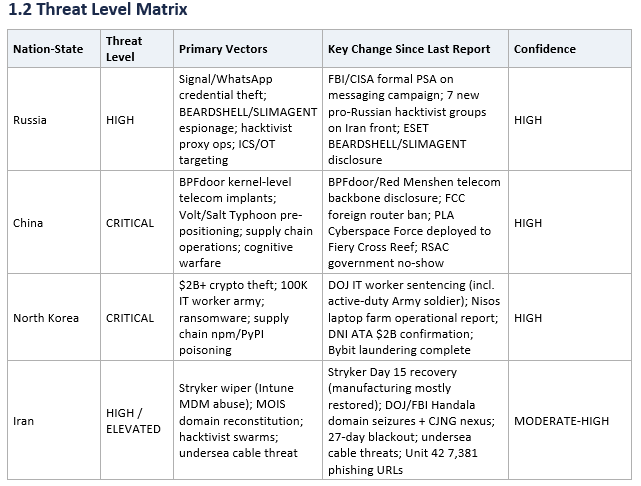
1.1 Key Judgments
• China remains the most persistent and technically advanced cyber threat. The March 26 disclosure of BPFdoor/Red Menshen kernel-level implants inside telecom backbone infrastructure worldwide reveals Chinese operators have penetrated below the IT layer where Salt Typhoon operated, embedding themselves in the signaling core of 4G/5G networks. This represents the most technically significant nation-state implant disclosure of the reporting period and underscores the inadequacy of perimeter-focused defenses.
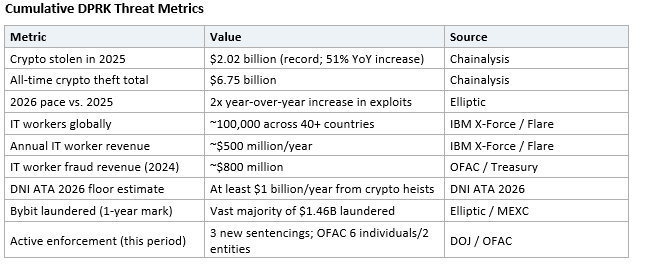
• North Korea has achieved strategic-scale financial theft through cyber operations. The DNI 2026 Annual Threat Assessment confirms DPRK stole over $2 billion in cryptocurrency in 2025 alone, a 51% year-over-year increase. IBM X-Force and Flare Research quantify approximately 100,000 DPRK IT workers deployed across 40+ countries generating $500 million annually. The Bybit $1.46 billion laundering operation is now substantially complete at the one-year mark, confirming DPRK’s ability to convert stolen digital assets into usable regime revenue.
• Russia’s intelligence services have compromised thousands of messaging app accounts globally. The FBI/CISA Joint PSA of March 20 formally attributed the Signal/WhatsApp account compromise campaign to Russian Intelligence Services, confirming U.S. government officials and military personnel are among victims. This is the largest Russian-linked intelligence collection operation against messaging platforms on record.
• Iran’s cyber capability is degraded but persistent, with escalating proxy operations. Despite 27 consecutive days of near-total internet blackout, Handala/MOIS restored operations within 24 hours of DOJ domain seizures. The Stryker Corporation wiper attack recovery has reached Day 15 with manufacturing mostly restored. Iran’s threat to sever Red Sea and Strait of Hormuz undersea cables introduces a new asymmetric global disruption risk.
• Russia-Iran convergence has escalated to confirmed military technology transfer. Russia is now actively shipping modified Shahed drone components and satellite imagery to Iran, confirmed by ISW and the EU Foreign Policy Chief. Pro-Russian hacktivist groups (seven newly identified) have expanded operations in support of Iran against Israeli and Western targets.
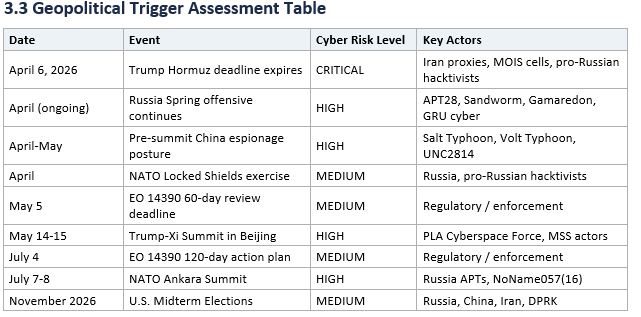
• The April 6 Trump Hormuz deadline represents the single highest-probability cyber escalation trigger in the next 30 days. If Iran fails to reopen the Strait of Hormuz, renewed U.S. energy infrastructure strikes could trigger an immediate surge in Iranian cyber retaliation, including wiper attacks against U.S. and allied targets. Unit 42 has formally elevated its wiper attack risk assessment.
• The Trump-Xi Summit is confirmed for May 14-15, creating a defined pre-summit espionage window. Chinese APT groups, particularly Salt Typhoon and Volt Typhoon, are expected to intensify intelligence collection operations over the next seven weeks to position Beijing with maximum negotiating leverage.
• Public-private partnership on China cyber defense is visibly straining. At RSAC 2026, FBI and NSA cancelled appearances on the flagship China Typhoon panel, leaving a literal empty chair. Combined with CISA staffing cuts and reduced engagement capacity, this signals structural weakening in U.S. defense coordination at a time of elevated threat activity.
1.3 Reporting Period Overview
This briefing covers the period from February 10 through March 27, 2026, updating and extending the March 20 baseline assessment with one week of new intelligence collection. The period encompasses some of the most consequential developments in the nation-state cyber threat landscape since Russia’s full-scale invasion of Ukraine in 2022.
The reporting window is defined by three intersecting crises: the ongoing Russia-Ukraine war and its associated sustained APT tempo against NATO allies; the U.S.-Israel-Iran military conflict (Operation Epic Fury/Roaring Lion), which triggered the most active multi-actor cyber environment since the Ukraine invasion; and China’s continued pre-positioning campaign against U.S. critical infrastructure, now extending to kernel-level implants inside telecom backbone systems. North Korea’s cyber-enabled financial theft operations have simultaneously reached unprecedented scale, with the intelligence community formally assessing DPRK revenue generation at its highest level since before 2018 sanctions.
The convergence of these threats is not incidental. Russia, China, Iran, and North Korea are operating with increasing inter-state alignment through shared infrastructure, coordinated timing, and mutual benefit from overlapping target sets. The Atlantic Council’s “Axis of Evasion” framework captures the emerging supply chain cooperation where drones, navigation systems, and cyber tools flow between these actors in a network that is greater than the sum of its parts.
1.4 Analytical Confidence and Methodology
This assessment adheres to Intelligence Community Directive 203 (ICD-203) standards for analytic tradecraft. Confidence levels are assigned based on the reliability, corroboration, and consistency of source reporting.
Source tiers used in this assessment:
• Tier 1: Government primary sources (FBI, CISA, DOJ, ODNI, NSA, AIVD/MIVD, ANSSI, OFAC). Highest confidence; formal attribution or enforcement action.
• Tier 2: Major cybersecurity vendor research and forensic analysis (CrowdStrike, Mandiant/Google GTIG, Microsoft MSTIC, Palo Alto Unit 42, Rapid7, ESET, Symantec, IBM X-Force). High confidence; independent technical verification.
• Tier 3: Trade press, journalism, and secondary vendor analysis (The Hacker News, BleepingComputer, SecurityWeek, The Register, Reuters, Bloomberg). Moderate confidence; reporting on primary sources.
• Tier 4: Social media, Telegram channels, hacktivist claims, and unverified intelligence (FalconFeedsio, X/Twitter posts, hacktivist group communications). Low confidence; requires corroboration.
Key analytic judgments use standardized probability language: “almost certainly” (95%+), “highly likely” (80-95%), “likely” (60-80%), “possible” (40-60%), “unlikely” (20-40%). Where confidence is explicitly stated as LOW or unverified, findings are included for situational awareness only and should not drive defensive resource allocation without corroboration.
PART 2: NATION-STATE THREAT ASSESSMENTS
2.1 Russia
2.1.1 Strategic Overview
Russia’s cyber posture during the reporting period reflects a mature, multi-layered hybrid warfare capability operating at sustained wartime tempo. The GRU (Military Intelligence Units 26165 and 74455), SVR (Foreign Intelligence Service), and FSB (Federal Security Service) are conducting parallel, operationally distinct campaigns spanning zero-day exploitation, large-scale credential theft against encrypted messaging platforms, critical infrastructure pre-positioning across NATO states, and coordinated influence operations. Russia’s New Generation Warfare (NGW) doctrine treats cyber operations as integral to combined arms operations, and the Spring 2026 offensive—assessed by ISW as having begun between March 17 and 21—ensures that APT tempo against Ukrainian and NATO targets will remain elevated for the foreseeable future.
The addition of pro-Russian hacktivist operations on the Iran war cyber front represents an opportunistic but operationally significant expansion of Russia’s cyber proxy ecosystem. While the Chatham House report (March 25) assesses that Russia’s cyber campaign against Ukraine has not achieved the strategic effects Moscow anticipated, the breadth and persistence of operations across at least seven major APT groups and dozens of hacktivist proxies confirms that Russia retains the most diversified and operationally active nation-state cyber apparatus in the world.
2.1.2 Key Developments This Period
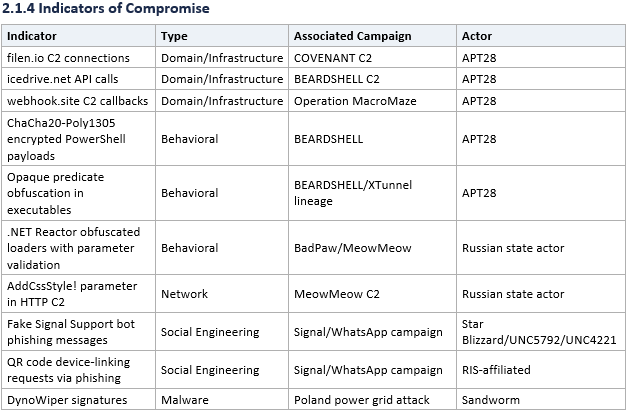
FBI/CISA Joint PSA on Signal/WhatsApp Campaign (March 20, 2026): The FBI and CISA issued their first formal Public Service Announcement (Alert I-032026-PSA) attributing an ongoing global phishing campaign against Signal and WhatsApp to Russian Intelligence Services (RIS). FBI Director Kash Patel confirmed “thousands of individual accounts” compromised worldwide, including current and former U.S. government officials, military personnel, political figures, and journalists. The campaign uses social engineering—actors pose as “Signal Support” bots to steal device-linking QR codes or account PINs—rather than breaking the apps’ encryption. Prior attribution by Microsoft and Google GTIG linked specific techniques to Star Blizzard (FSB), UNC5792/UAC-0195 (assessed GRU-linked), and UNC4221/UAC-0185 (assessed GRU-linked). The PSA warns that the campaign may evolve to include malware deployment.
ANSSI/France Advisory (March 20-21, 2026): France’s Cyber Crisis Coordination Center (C4/ANSSI) independently corroborated the messaging app campaign, warning of a surge targeting French government officials, journalists, and business leaders. This extends the confirmed targeting footprint to four core EU/NATO countries: the United States, France, Germany, and the Netherlands.
ESET BEARDSHELL/SLIMAGENT Disclosure (March 10, 2026): ESET published the full technical details of an APT28 long-term espionage campaign against Ukrainian military personnel using three paired implants: BEARDSHELL (backdoor/loader using Icedrive cloud API for C2 with ChaCha20-Poly1305 encryption), COVENANT (heavily modified open-source post-exploitation framework using Filen cloud storage for C2), and SLIMAGENT (keylogger/screenshot tool with code lineage to APT28’s XAgent from the 2016 DNC hack). The dual-cloud-provider C2 architecture demonstrates redundancy design—blocking one cloud service does not disable the campaign. Campaign active since April 2024 with forensic analysis conducted jointly with CERT-UA and Ukrainian Military Unit A0334.
ClearSky BadPaw/MeowMeow Campaign (March 3, 2026): ClearSky disclosed a targeted Russian campaign against Ukrainian entities using two previously undiscovered malware strains: BadPaw (.NET loader with Reactor obfuscation and decoy GUI) and MeowMeow (sophisticated backdoor with remote PowerShell execution, VM detection, and monitoring tool scanning for Wireshark, ProcMon, and OllyDbg). The malware uses a staged C2 mechanism with encrypted data via AddCssStyle! parameter. Russian-language strings in MeowMeow code confirm Russian state attribution with high confidence; specific APT28 attribution is assessed with low confidence.
DOJ TA551 Sentencing (March 24, 2026): The DOJ sentenced Ilya Angelov, 40, of Tolyatti, Russia, to 24 months in federal prison for co-managing the TA551 botnet (also tracked as Mario Kart, Shathak, GOLD CABIN). TA551 sold botnet access to ransomware operators including BitPaymer, enabling $14.17 million in extortion payments from 72 U.S. corporations. A separate Russian national, Aleksei Volkov, received nearly 7 years for serving as an initial access broker for Yanluowang ransomware attacks. While TA551 is cybercriminal rather than state-sponsored, it operates within the Russian criminal ecosystem that provides infrastructure and access to GRU/FSB-affiliated groups.
Pro-Russian Hacktivist Escalation on Iran Front (March 2026): Seven additional pro-Russian hacktivist groups—Cardinal, Russian Legion, Hider_Nex, RuskiNet, PalachPro, Dark Storm Team, and Server Killers—have joined operations in support of Iran against Israeli and Western targets. Claims include Iron Dome radar infiltration (Cardinal/Russian Legion—assessed as highly exaggerated by Intel 471 and Trellix), Israeli water system HMI access (Z-Pentest Alliance), and Israeli bank DDoS (Dark Storm Team). Resecurity assesses the activity is “uncoordinated and conducted by multiple disconnected groups” rather than centrally directed, despite Kremlin messaging suggesting alignment. Unit 42 confirms approximately 60 hacktivist groups remain active on the Iran front as of March 26.
Gamaredon Sustained Tempo: CERT-UA continues to assess Gamaredon (Aqua Blizzard/UAC-0010) as the highest-volume Russian APT group targeting Ukraine, with continuous phishing and removable-drive infection campaigns. Gamaredon’s GammaSteel data exfiltration tool and USB propagation techniques remain active throughout the reporting period.
Secret Blizzard/Turla Supply Chain: The FSB’s Turla group continues ISP-level adversary-in-the-middle (AiTM) operations against diplomatic targets, with ESET confirming collaboration between Gamaredon and Turla where Turla exploits Gamaredon infections to deploy its own more sophisticated implants—a form of internal Russian intelligence supply chain.
APT28/APT29 NATO Operations: APT28 (Forest Blizzard/GRU Unit 26165) conducted at least three distinct campaigns during the period: Operation Neusploit exploiting CVE-2026-21509 (Microsoft Office OLE bypass, CVSS 8.8, weaponized within 24-72 hours of patch); Operation Silent Rendering exploiting CVE-2026-21513 (MSHTML zero-day against Eastern European governments); and Operation MacroMaze using webhook.site for C2 against European entities. APT29 (Midnight Blizzard/SVR) sustained identity-based intrusions and RDP-based spearphishing campaigns against NATO allied government and defense targets.
Sandworm/Seashell Blizzard ICS/OT Targeting: Sandworm (GRU Unit 74455/APT44) continues targeting critical infrastructure across NATO states, with the DynoWiper attack on Poland’s power grid (January 2026) representing the most significant known Sandworm operation of the period. The BadPilot subgroup maintains initial access operations against network edge devices. Sandworm’s ZeroLot wiper deployment against Ukrainian energy companies during 2024-2025 confirms ongoing wiper capability development.
Midnight Blizzard Phishing Campaigns: APT29’s Midnight Blizzard continues high-volume phishing campaigns using signed RDP configuration files to establish persistent access to NATO government networks. Microsoft and Picus Security track this as an ongoing operational campaign with identity-based intrusions across multiple allied government targets.
2.1.3 Tactics, Techniques, and Procedures (TTPs)
Russian APT groups employed the following primary TTP clusters during the reporting period:
• Zero-day and rapid exploitation: APT28 demonstrated sub-72-hour weaponization of CVE-2026-21509 and pre-patch exploitation of the MSHTML zero-day CVE-2026-21513, reflecting elite vulnerability exploitation capability.
• Cloud-based C2: Multiple campaigns leverage legitimate cloud services for command and control, including Filen (COVENANT), Icedrive (BEARDSHELL), webhook.site (Operation MacroMaze), and Google services. This approach evades network-level detection by hiding C2 traffic within legitimate HTTPS connections.
• Social engineering against messaging platforms: The Signal/WhatsApp campaign exploits user trust in platform support infrastructure. Actors create urgency through fake “suspicious activity” notifications, then steal device-linking codes that grant full historical message access. MITRE ATT&CK: T1566.004, T1676, T1078, T1534.
• Living-off-the-land and identity abuse: APT29 and associated groups increasingly exploit legitimate identity management tools (RDP, Azure AD, Entra ID) rather than deploying custom malware, complicating detection.
• Hacktivist proxy operations: Pro-Russian groups conduct DDoS, website defacement, and claimed OT/ICS access operations that provide Russia plausible deniability while amplifying psychological effects. MITRE ATT&CK: T1498, T1491.
• Wiper deployment: Sandworm’s DynoWiper and ZeroLot demonstrate continued investment in destructive capability against critical infrastructure. MITRE ATT&CK: T1485, T1561.
2.1.5 Assessment and Outlook
Russia’s cyber threat posture is assessed as HIGH and trending UPWARD. The FBI/CISA PSA represents the strongest U.S. government signal to date that Russian intelligence has achieved significant scale in compromising encrypted messaging accounts of high-value targets. The dual-cloud C2 architecture revealed in the BEARDSHELL/COVENANT campaign demonstrates APT28’s continued operational sophistication, while the expanding hacktivist proxy ecosystem on the Iran front shows Russia’s willingness to leverage the multi-front conflict environment for opportunistic operations.
Looking ahead 30-90 days: Russia’s Spring 2026 offensive will sustain elevated APT tempo against Ukraine and NATO allies. The messaging app campaign will likely continue and may incorporate malware deployment per the FBI/CISA warning. French municipal elections (March 2026) create additional targets for Storm-1516 influence operations. Defenders should prioritize Signal/WhatsApp device audit, cloud storage service monitoring for Icedrive/Filen/webhook.site, and OT/ICS exposure validation against hacktivist reconnaissance.
2.2 China
2.2.1 Strategic Overview
The Office of the Director of National Intelligence (ODNI) 2026 Annual Threat Assessment identifies China as “the most active and persistent cyber threat to U.S. government, private-sector, and critical infrastructure networks.” China’s cyber operations in this reporting period demonstrate an unmistakable pattern of escalation in both technical sophistication and strategic ambition. The PRC’s cyber apparatus—spanning the Ministry of State Security (MSS), People’s Liberation Army (PLA), and a deepening ecosystem of private contractor companies—is conducting simultaneous campaigns across telecom infrastructure, critical infrastructure pre-positioning, supply chain compromise, and cognitive warfare targeting Taiwan.
The March 26 disclosure of BPFdoor implants inside telecom backbone infrastructure represents a qualitative leap beyond previous publicly documented China APT operations. While Salt Typhoon targeted the IT layer—call records, lawful intercept systems—Red Menshen is operating below that, embedding kernel-level implants in the signaling core of systems that constitute the telecom infrastructure itself. The FCC’s blanket ban on foreign-manufactured routers, announced the same week, underscores the scale of the policy response—but as security analysts noted, the policy is “catching up to one problem while the adversary has already moved on to the next.”
The confirmed rescheduling of the Trump-Xi Summit to May 14-15 creates a defined seven-week espionage posture window. Historical patterns demonstrate that Chinese cyber operations intensify before diplomatic engagements to maximize intelligence leverage for negotiations on tariffs, AI chip access, Taiwan arms sales, and trade normalization.
2.2.2 Key Developments This Period
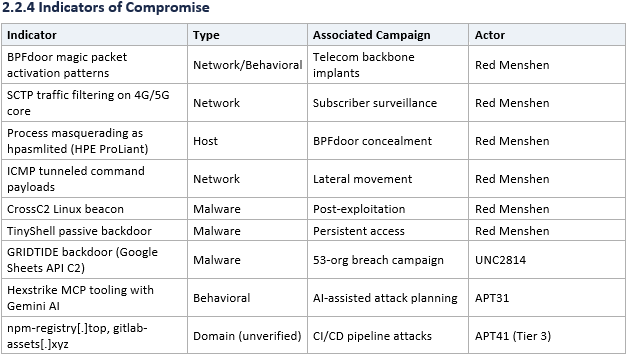
BPFdoor/Red Menshen Kernel-Level Telecom Implants (March 26, 2026 — CRITICAL): Rapid7 published research revealing that Red Menshen, a China-nexus group distinct from the named Typhoon families, has deployed BPFdoor—a passive kernel-level Linux backdoor—deep inside the signaling core of telecom backbone infrastructure worldwide. BPFdoor abuses Berkeley Packet Filter functionality to inspect network traffic inside the kernel. It opens no ports, does not beacon home, and does not appear in netstat or standard monitoring tools, remaining completely dormant until activated by a specifically crafted “magic packet.” New variants include HTTPS-embedded activation using a “magic ruler” technique that places command markers at the 26th byte offset (surviving TLS termination), SCTP signaling filters targeting 4G/5G core networks for passive subscriber identity surveillance, and ICMP tunneling for lateral movement. Targets include U.S., Canadian, European, and Asian telecom providers. Deployed alongside CrossC2, TinyShell, custom keyloggers, and SSH brute-force utilities with telecom-specific credential lists. Initial access via known CVEs in Ivanti, Cisco, Fortinet, VMware, and Palo Alto Networks appliances. Rapid7 released a BPFdoor scanning script for defenders.
FCC Router Ban (March 23, 2026): The Federal Communications Commission formally banned all new imports of foreign-made consumer routers, explicitly citing Volt Typhoon, Flax Typhoon, and Salt Typhoon operations. The White House-convened interagency determination stated that foreign-produced routers pose “a severe cybersecurity risk that could be leveraged to immediately and severely disrupt U.S. critical infrastructure.” The FCC also cited CovertNetwork-1658 (Quad7 botnet) operated by Storm-0940. China controls approximately 60% of the U.S. home router market. The ban applies to new device models seeking FCC authorization; existing devices are not recalled. Starlink Wi-Fi routers (manufactured in Texas) are exempt.
RSAC 2026 “Empty Chair” (March 23, 2026): At RSA Conference 2026, FBI and NSA speakers cancelled their participation in a panel titled “Inside the Hunt for China’s Typhoons: Disrupt, Deter, and Defend.” The government’s no-show—represented by a literal empty chair on stage—became a symbol of strained public-private partnership on China threat response. Private-sector panelists (from Palo Alto Networks, EY, and Sidley Austin) noted that Volt and Salt Typhoon response required private-sector intelligence sharing for the government to act, and that the empty chair “is not a good look” at a time of elevated threat.
EU Sanctions on Integrity Technology/i-Soon (March 16, 2026): The European Union formally sanctioned Integrity Technology Group (linked to Flax Typhoon botnet) and Anxun Information Technology (i-Soon, the Chinese hacking contractor whose internal documents leaked in February 2024). This represents the most significant expansion of the EU’s cyber sanctions regime since its creation in 2019. The designations align with prior U.S. Treasury OFAC sanctions, representing growing transatlantic coordination on China cyber attribution.
PLA Cyberspace Force Deployment to Fiery Cross Reef (February 12, 2026): Xi Jinping’s Lunar New Year video message publicly revealed for the first time a PLA Cyberspace Force unit stationed on Fiery Cross Reef in the disputed Spratly Islands. This deployment places Chinese state cyber operators in closer physical proximity to undersea cable infrastructure, regional telecommunications nodes, and military networks of U.S. allies including the Philippines, Vietnam, and Malaysia. The section chief stated: “We shall remain constantly ready for action.”
Salt Typhoon Telecom Infiltration: The FBI confirmed on February 19 that Salt Typhoon intrusions remain “still very, very much ongoing,” spanning 200+ companies across 80+ countries. AT&T and Verizon have not confirmed full eviction. Salt Typhoon has compromised lawful intercept systems at nine or more U.S. telecommunications carriers, enabling access to call records, metadata, and in some cases live communications of senior U.S. government officials.
Volt Typhoon Critical Infrastructure Pre-Positioning: Dragos elevated VOLTZITE (Volt Typhoon) to Stage 2 of the ICS Cyber Kill Chain in February 2026, confirming the group has moved from IT reconnaissance into operational technology (OT) environments—specifically extracting alarm configurations, process shutdown parameters, and control loop diagrams from U.S. utilities. This represents confirmed pre-positioning for potential destructive operations against U.S. energy infrastructure.
Silk Typhoon Supply Chain Operations: UNC6201/Silk Typhoon continues exploitation of CVE-2026-22769 (Dell zero-day) for supply chain compromise operations targeting defense and technology sectors.
GoLaxy Cognitive Warfare Database (March 2026): Leaked documents from PRC state-affiliated firm GoLaxy—spun off from the Chinese Academy of Sciences—reveal a database compiled on 170 Taiwanese politicians (including President Lai), all 23 million Taiwanese household registration records, and databases of U.S. political figures. The system powers AI-driven “smart propaganda” using bots for targeted cognitive warfare, with funding and guidance sought from the Cyberspace Administration of China, Central Propaganda Department, and Ministry of State Security.
Taiwan 2.63 Million Daily Attacks: Taiwan’s National Security Bureau reported Chinese cyberattacks on Taiwan’s critical infrastructure averaged 2.63 million per day in 2025, a 6% year-over-year increase and 113% increase since the 2023 baseline. Attacks correlated with 23 of 40 PLA “joint combat readiness patrols,” confirming hybrid threat doctrine integration. Taiwan’s undersea cable vulnerability is severe: severing three cable clusters near Bashi Channel could reduce international bandwidth by 95%, with no indigenous cable repair capability and peacetime repair time exceeding 40 days.
2.2.3 Tactics, Techniques, and Procedures
• Kernel-level implant deployment: BPFdoor operates at the Berkeley Packet Filter level inside the Linux kernel, using magic packets for dormant activation. No ports opened, no beaconing, invisible to standard monitoring. MITRE ATT&CK: T1014 (Rootkit), T1205 (Traffic Signaling).
• Living-off-the-land at infrastructure level: Volt Typhoon and Red Menshen exploit legitimate system tools and protocols (SCTP, ICMP, hardware management daemons) to operate within normal network behavior. MITRE ATT&CK: T1218.
• Edge device exploitation: Consistent exploitation of known vulnerabilities in network appliances from Ivanti, Cisco, Fortinet, VMware, and Palo Alto Networks for initial access. MITRE ATT&CK: T1190.
• Lawful intercept compromise: Salt Typhoon targets carrier-grade lawful intercept systems to access communications metadata and content of surveillance targets. MITRE ATT&CK: T1557.
• Botnet construction: Flax Typhoon/Integrity Technology operated hundreds of thousands of compromised IoT devices for distributed operations. Storm-0940/CovertNetwork-1658 uses compromised routers for credential spraying.
• AI-enabled cognitive warfare: GoLaxy database enables ML-driven targeting and propaganda generation for influence operations against Taiwan and U.S. political figures.
• Supply chain poisoning: APT41 reportedly targeting semiconductor CI/CD pipelines (Tier 3, unverified) through poisoned npm/PyPI packages.
2.2.5 Assessment and Outlook
China’s cyber threat level is assessed as CRITICAL and ESCALATING. The BPFdoor disclosure demonstrates that China’s most capable groups have moved further down the technology stack than previously documented, operating at the kernel level inside telecom backbone infrastructure. Combined with Salt Typhoon’s ongoing presence in 200+ companies, Volt Typhoon’s Stage 2 OT access, and the FCC’s emergency router ban, the evidence points to a comprehensive Chinese strategy to establish persistent, deeply embedded access across U.S. and allied critical infrastructure.
The 30-90 day outlook is dominated by the May 14-15 Trump-Xi Summit. Espionage operations will intensify as Beijing positions for maximum negotiating leverage on tariffs, AI chip access, and trade normalization. Taiwan cyber pressure will continue at or above the 2.63 million daily attack baseline, with GoLaxy cognitive warfare capabilities representing a qualitative enhancement to PRC influence operations. Defenders should prioritize BPF filter enumeration, raw socket auditing, and process integrity validation on Linux systems, particularly in telecom and critical infrastructure environments.
2.3 North Korea
2.3.1 Strategic Overview
North Korea’s cyber program has achieved a scale and sophistication that places it among the most consequential nation-state cyber threats globally. The DNI 2026 Annual Threat Assessment—the U.S. intelligence community’s authoritative public assessment—characterizes DPRK cyber capabilities as “sophisticated and agile” and confirms that cryptocurrency theft, IT worker fraud, and ransomware collectively represent Pyongyang’s primary sanctions evasion mechanisms. DPRK foreign currency revenue generation is at its highest level since before extensive sanctions were imposed in 2018, driven by the convergence of Russia military payments, cyber theft, and IT worker salary extraction.
The DPRK cyber apparatus operates across multiple distinct but strategically coordinated threat groups: Lazarus Group/Stonefly (ransomware, crypto theft, defense espionage), BlueNoroff/Sapphire Sleet (financial theft, cryptocurrency targeting), Kimsuky/Emerald Sleet (intelligence collection, quishing campaigns), Famous Chollima/Coral Sleet (IT worker fraud, supply chain poisoning), and APT37/ScarCruft (air-gap bridging, intelligence collection). These groups share infrastructure and objectives while maintaining operational separation that complicates attribution and response.
2.3.2 Key Developments This Period
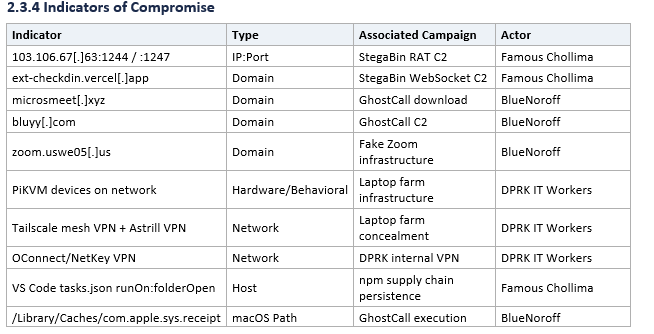
DOJ IT Worker Facilitator Sentencing Including Active-Duty Army Soldier (March 20, 2026): The U.S. District Court for the Southern District of Georgia sentenced three defendants for operating laptop farms enabling North Korean IT worker access to U.S. company networks. Alexander Paul Travis, 35, an active-duty U.S. Army soldier stationed at Fort Gordon (home to U.S. Army Cyber Command), received 12 months in federal prison for renting his identity to DPRK workers for approximately three years beginning September 2019. Travis passed employer vetting on behalf of DPRK workers including drug tests, fingerprinting, and video interviews, opened bank accounts to funnel salaries, and ran a laptop farm from his Augusta residence. Jason Salazar and Audricus Phagnasay received 3 years probation each for facilitating $1.28 million in salary payments. The compromise of a U.S. Army soldier at the home base of Cyber Command demonstrates DPRK’s ability to recruit military personnel as witting insider threats.
Nisos Laptop Farm Operational Report (March 20, 2026): Cybersecurity firm Nisos published the most detailed technical view of DPRK laptop farm infrastructure to date, based on monitoring a suspected DPRK IT worker candidate targeting their own hiring pipeline. Key findings include: approximately 40 devices on a single farm’s local network with 20 actively used as remote-controlled endpoints; confirmed use of PiKVM (Keyboard-Video-Mouse over IP) devices for hardware-level remote control that evades corporate EDR; Tailscale mesh VPN and Astrill VPN for concealment; real-time AI overlay generating interview answers during live video calls; and canary token deployment capturing physical images of the farm. Nisos assesses hundreds of similar laptop farms operate across the United States.
DNI 2026 Annual Threat Assessment — $2 Billion Stolen (March 18, 2026): DNI Tulsi Gabbard released the 2026 ATA confirming that DPRK stole “$2 billion in cryptocurrency in 2025 alone” and assessing that crypto heists “continue to net at least $1 billion each year” as a floor estimate. The ATA explicitly elevates the IT worker insider threat as a distinct threat vector alongside direct cyber attacks, noting DPRK’s “growing use of human insider access to circumvent cyber security measures threatens targets with stronger defensive measures.” The ATA data cutoff is March 14, 2026, making it the most current IC assessment available.
IBM X-Force/Flare Research — 100,000 IT Workers, $500 Million/Year (March 18, 2026): The most comprehensive scale assessment of the DPRK IT worker scheme reveals approximately 100,000 North Korean IT workers deployed across 40+ countries, generating roughly $500 million annually. The scheme operates through a four-tier model: Recruiters who screen candidates, Facilitators who maintain fake company identities (”C Digital LLC” is a common cover), IT Workers with full-stack development skills who often have multiple people supporting a single fake employee, and Collaborators/Brokers (Western nationals providing identities recruited via LinkedIn/GitHub). Technical tools confirmed: OConnect/NetKey (North Korean proprietary VPN), IP Messenger for peer communications, Google Translate for all work, and AI face/voice changers for video interviews. When discovered, workers escalate through demands for access reinstatement, threats to sell data to competitors, and claims of residual access with handoff to DPRK APT groups.
Bybit $1.46 Billion Laundering Complete at One-Year Mark (March 23, 2026): Multiple blockchain analytics firms confirm the vast majority of the $1.46 billion stolen from Bybit on February 21, 2025—the largest confirmed cryptocurrency theft in history—has been successfully laundered by the one-year anniversary. Laundering pathways included DeFi protocols (immediate conversion), mixing services, Chinese-language OTC traders, and no-KYC exchanges. At least $1 billion was laundered within the first six months. The Bybit theft accounted for 69% of all crypto-service losses industry-wide in 2025. CSIS published analysis calling for updated U.S. crypto regulation in response.
Contagious Interview/StegaBin Campaign (Famous Chollima): The March 2 StegaBin variant deployed 26 malicious npm packages using character-level steganography in Pastebin for C2 encoding, with RAT C2 at 103.106.67[.]63 ports 1244/1247 and WebSocket C2 at ext-checkdin.vercel[.]app. Famous Chollima continues operating multiple parallel npm campaign techniques simultaneously, targeting developer environments through VS Code tasks.json persistence with malicious runOn triggers.
Lazarus/BlueNoroff Bitrefill Breach (March 2026): The cryptocurrency gift card platform Bitrefill was breached in an operation attributed with high confidence to a BlueNoroff/Lazarus subdivision. The full scope of compromise is not yet publicly disclosed.
Kimsuky Quishing Campaign (Ongoing): Kimsuky/Emerald Sleet continues an ongoing QR-code phishing (quishing) campaign against U.S. think tanks, NGOs, and government entities. The FBI issued formal FLASH advisory AC-000001-MW in January 2026 and activity is assessed as continuing throughout the reporting window.
APT37 Ruby Jumper Air-Gap Campaign (February 27, 2026): Zscaler reported a new APT37/ScarCruft campaign designated Ruby Jumper deploying five previously undocumented tools specifically designed to bridge air-gapped systems. This capability is significant as it targets the most secure network environments used by military, intelligence, and critical infrastructure operators.
Lazarus Medusa Ransomware (February 24, 2026): Symantec confirmed Lazarus Group/Stonefly deployment of Medusa ransomware-as-a-service against U.S. healthcare targets and Middle East organizations, representing continued expansion of DPRK’s ransomware portfolio as a revenue generation mechanism.
OFAC March 12 Sanctions: The U.S. Treasury sanctioned 6 individuals, 2 entities, and designated 21 cryptocurrency wallet addresses linked to DPRK IT worker fraud generating nearly $800 million in 2024.
2.3.3 Tactics, Techniques, and Procedures
• IT worker infiltration: Four-tier model using stolen/rented U.S. identities, PiKVM hardware for remote laptop control, Tailscale/Astrill VPN concealment, AI-generated interview responses, and physical laptop farms across the United States. MITRE ATT&CK: T1078 (Valid Accounts), T1219 (Remote Access Software).
• Cryptocurrency theft: Targeting DeFi platforms, centralized exchanges, and cryptocurrency service providers through sophisticated social engineering (Operation Dream Job), supply chain compromise (npm/PyPI poisoning), and direct infrastructure exploitation. MITRE ATT&CK: T1657 (Financial Theft).
• Supply chain poisoning: Malicious npm and PyPI packages using steganographic C2 encoding, VS Code persistence mechanisms, and character-level encoding in Pastebin. MITRE ATT&CK: T1195.002 (Supply Chain Compromise: Compromise Software Supply Chain).
• Air-gap bridging: APT37 Ruby Jumper deploying purpose-built tools to cross air-gapped network boundaries, targeting military and intelligence environments.
• Ransomware-as-a-Service: Lazarus deployment of commodity ransomware (Medusa) for dual-purpose revenue generation and intelligence access.
• Quishing: QR-code phishing targeting mobile devices to bypass traditional email security controls. MITRE ATT&CK: T1566.002.
• Multi-stage laundering: Sophisticated cryptocurrency laundering via DeFi-to-mixer-to-OTC-to-fiat pipeline with Chinese OTC traders as key intermediary layer.
2.3.5 Assessment and Outlook
North Korea’s cyber threat level is assessed as CRITICAL AND SUSTAINED. The convergence of $2+ billion in annual cryptocurrency theft, approximately 100,000 deployed IT workers, expanding ransomware operations, and purpose-built air-gap bridging tools makes DPRK one of the two most consequential nation-state cyber threats (alongside China) during this reporting period.
The 30-90 day outlook: DPRK is expected to maintain current operational tempo across all vectors. The successful completion of Bybit laundering demonstrates that DPRK has refined its financial conversion pipeline to handle billion-dollar-scale theft efficiently. New cryptocurrency platform compromises should be anticipated. The IT worker threat requires sustained attention, as the Travis case demonstrates DPRK’s willingness to recruit military personnel and the Nisos report reveals the physical infrastructure supporting these operations at scale.
2.4 Iran
2.4.1 Strategic Overview
The reporting period encompasses the most consequential shift in Iranian cyber operations since the Shamoon attacks of 2012. The February 28, 2026 U.S.-Israel coordinated military offensive—Operation Epic Fury (U.S.) and Operation Roaring Lion (Israel)—triggered an immediate, multi-vector Iranian retaliatory cyber campaign that fundamentally transformed the landscape from pre-war espionage to hybrid warfare combining hacktivist swarms, MOIS-directed wiper operations, and critical infrastructure targeting.
Iran has now surpassed 27 consecutive days of near-total internet blackout (approximately 1% connectivity per NetBlocks), the most extensive digital blackout in the world. This has severely degraded coordinated state APT operations from within Iran but has not eliminated the threat—MOIS-linked cells operating outside Iran retain autonomous capability, as demonstrated by Handala’s sub-24-hour reconstitution after DOJ domain seizures. The confirmed strike on IRGC cyberwarfare headquarters in Tehran and the killing of MOIS Deputy Minister Seyed Yahya Hosseiny Panjaki represent partial decapitation of Iran’s cyber command authority, but dispersed operations continue under increased tactical autonomy.
Multiple authoritative analyses (Lawfare, CSIS) converge on the assessment that the current conflict, by destroying Iran’s conventional military deterrence options, is likely to produce a more formidable and motivated Iranian cyber threat in the post-war period—potentially following the North Korea trajectory of cyber as strategic economic weapon and power projection tool.
2.4.2 Key Developments This Period
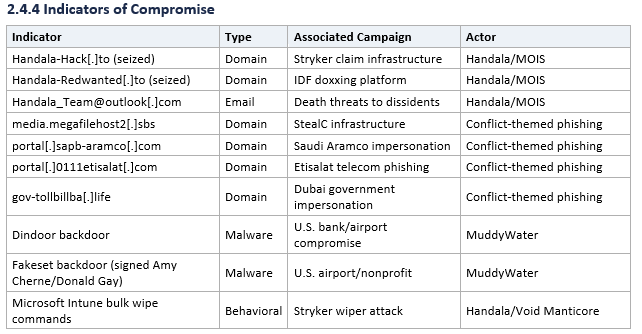
DOJ/FBI Handala/MOIS Domain Seizures + CJNG Cartel Nexus (March 19, 2026): The Department of Justice seized four domains linked to Iran’s Ministry of Intelligence and Security: Handala-Hack[.]to (primary operational domain used to claim the Stryker attack), Handala-Redwanted[.]to (doxxing platform with 190+ IDF personnel data), Justicehomeland[.]org, and Karmabelow80[.]org. The FBI affidavit revealed MOIS explicitly solicited the Mexican CJNG (Jalisco New Generation Cartel) as “partners” to commit physical violence against Iranian dissidents on U.S. and Canadian soil—a new escalation representing Iran’s first documented attempt to weaponize transnational criminal organizations for physical threats against diaspora targets in North America.
Handala Sub-24-Hour Reconstitution (March 20, 2026): Within approximately 24 hours of DOJ domain seizures, Handala restored its online presence on a new domain. Security experts assessed the seizure had “negligible operational impact” and that infrastructure-focused takedown operations are fundamentally insufficient to degrade MOIS-directed hacktivist operations. Handala publicly stated the seizures were “attempts by the United States and its allies to silence the voice of Handala.”
Stryker Recovery Update — Day 15 (March 26, 2026): Stryker Corporation confirmed that manufacturing operations are “mostly restored” 15 days after the March 11 wiper attack. The investigation, conducted with Palo Alto Networks Unit 42, confirmed the core attack vector: Microsoft Intune exploited for administrator-level device management plane access, enabling bulk wipe commands to 200,000+ devices globally without deploying self-propagating malware. A “malicious file” was used to run commands enabling activity concealment. Stryker stock rose 2% on the recovery announcement. The attack remains the first confirmed destructive wiper operation against a U.S. Fortune 500 company.
Unit 42 March 26 Update — 7,381 Phishing URLs, Elevated Wiper Risk: Unit 42 issued a significant update tracking 7,381 phishing URLs across 1,881 unique hostnames exploiting conflict lures for financial fraud, credential harvesting, and cryptocurrency scams. Attack evasion techniques include TLD rotation, subdomain chaining, and purpose-built portals mimicking government/corporate payment workflows. Targets include UAE enterprises (Emirates brand), Saudi organizations (ERP impersonation), Gulf telecoms, and Iranian diaspora banking. Unit 42 is explicitly tracking elevated wiper attack risk, noting the Stryker pattern is a replicable template and Iranian “Serpens” actor cluster could escalate in coming weeks.
FBI Handala TTP Advisory (March 24, 2026): The FBI issued a formal warning detailing Handala’s malware chain targeting dissidents and journalists: Stage 1 malware disguised as Pictory, KeePass, WhatsApp, or Telegram; Stage 2 connects to Telegram C2 bots enabling remote access, screen capture exfiltration, and file theft. Handala performs target reconnaissance before engagement and tailors Stage 1 to each victim’s pattern of life.
Undersea Cable Threat (March 24, 2026): Iran is reportedly threatening to cut undersea internet cables in the Red Sea and Strait of Hormuz as coercive leverage against Gulf states hosting U.S. troops. The threatened cables carry approximately 17-18% of global internet traffic. At least 17 submarine cables run through the Red Sea; critical systems in the Strait of Hormuz include AAE-1, Falcon, and Gulf Bridge International Cable System. Meta and partners have paused work on the 2Africa Pearls cable due to Persian Gulf conflict zone risks. In 2024-2025, Houthi forces severed multiple Red Sea cables. The Strait’s depth (approximately 200 feet at the narrowest point) makes cables physically accessible. This represents Iran’s most asymmetric and globally disruptive non-kinetic option.
MuddyWater Exposed Directories / U.S. Bank and Airport Compromised (March 2026): eSentire published findings from publicly exposed open directories linked to MuddyWater, revealing tools, exploits, targeting information, and C2 details. Current targets include Israeli healthcare, Jordanian government webmail, Egyptian national airline, UAE enterprises, and critically, a U.S.-based technology company. Symantec/Carbon Black confirmed MuddyWater backdoors (Dindoor and Fakeset) embedded in a U.S. bank, U.S. airport, and Canadian nonprofit since February 2026. Activity continued after the February 28 strikes, indicating MuddyWater operations are not dependent on Iranian domestic connectivity.
CyberAv3ngers Reactivation (March 2026): IRGC Cyber-Electronic Command’s CyberAv3ngers reactivated in February/March 2026, conducting active scanning for vulnerable cameras and industrial equipment for reconnaissance and battle-damage assessment. Hikvision CVEs CVE-2017-7921, CVE-2021-36260, CVE-2023-6895, CVE-2025-34067 and Dahua CVE-2021-33044 are being actively exploited. Expanded OT targeting includes water/wastewater PLCs, LNG infrastructure, and energy sector broadly.
Cotton Sandstorm Gulf Operations: Cotton Sandstorm/Emennet Pasargad/Altoufan Team continues wiper and fake-ransomware operations in Bahrain and the Gulf region, using ASPX web shells, LOTL post-exploitation, and the WezRat infostealer.
Pioneer Kitten Ransomware Incentivization: State-sponsored actors are offering financial incentives to ransomware operators targeting U.S. and Israeli organizations, extending Pioneer Kitten’s established affiliate relationships (NoEscape, Ransomhouse, ALPHV/BlackCat) in the conflict context. Compromised cloud resources are being used for follow-on operations against U.S. academic and defense sector entities.
Cyber Isnaad Front (New Group): A newly identified coordination entity emerged around March 2026, targeting Israeli critical infrastructure and telecom providers with a public “hit list” of individuals across multiple industries.
Qatari LNG Targeting (March 2026): Security researchers observed confirmed claims of targeted operations against Qatari LNG facilities at Ras Laffan (world’s largest LNG production site) and Mesaieed (industrial/petrochemical city). Qatar hosts Al Udeid Air Base, the major U.S. military hub in the region.
IRGC Cyber HQ Confirmed Struck: Multiple sources (CSIS, Lawfare, The Soufan Center) confirm the IRGC cyberwarfare headquarters in Tehran was struck early in the conflict. Effect: near-term degradation of coordinated high-end APT operations, but not elimination of capability. Cells outside Iran have increased autonomous authority.
MOIS Deputy Minister Killed: Seyed Yahya Hosseiny Panjaki, Deputy Minister of Iran’s MOIS (which controls Handala and other MOIS hacking groups), confirmed killed in strikes. FBI-wanted Iranian hacker Mohammad Mehdi Farhadi Ramin also reported killed.
Senate SASC Cyber Hearing (March 24, 2026): DoD CIO Kirsten Davies and DISA Director Lt. Gen. Stanton testified before the Senate Armed Services Committee cybersecurity subcommittee on enterprise security under Operation Epic Fury. DoD requested $15.1 billion for cyber programs in FY2026.
FINRA Financial Sector Alert (March 2026): FINRA issued an industry-wide alert on heightened threats from Iranian cyber actors to the financial services sector, noting Evil Markhors claims against Israeli banks and DieNet claims against Riyadh Bank and Bank of Jordan.
2.4.3 Tactics, Techniques, and Procedures
• MDM/RMM management plane abuse: The Stryker attack weaponized Microsoft Intune to issue bulk factory reset commands, evading EDR entirely. This “Era of Identity Weaponization” represents a structural shift from compiled wiper malware to living-off-the-land abuse of device management infrastructure. MITRE ATT&CK: T1072 (Software Deployment Tools).
• Telegram-based C2: Handala uses Telegram bots for command and control of deployed malware, leveraging the platform’s encrypted communications and resistance to takedown. MITRE ATT&CK: T1102 (Web Service).
• Multi-stage malware targeting dissidents: Handala’s customized approach uses social engineering tailored to individual targets’ patterns of life, with Stage 1 disguised as common applications and Stage 2 providing full remote access.
• Camera network exploitation for BDA: CyberAv3ngers exploit unpatched Hikvision and Dahua cameras for real-time intelligence collection and battle-damage assessment. MITRE ATT&CK: T1595 (Active Scanning).
• Hacktivist swarm tactics: The Islamic Resilience Cyber Axis coordinates 60+ groups for simultaneous DDoS, defacement, and claimed OT access operations. MITRE ATT&CK: T1498, T1491.
• Ransomware collaboration model: Pioneer Kitten provides initial access to ransomware affiliates with state-provided financial incentives, blending state-directed objectives with criminal operations.
• Infrastructure reconstitution: Sub-24-hour domain restoration after government seizure, demonstrating operational resilience and pre-positioned contingency infrastructure.
2.4.5 Assessment and Outlook
Iran’s cyber posture is assessed as DEGRADED BUT PERSISTENT, WITH ESCALATING PROXY OPERATIONS. The 27-day internet blackout, IRGC cyber HQ strike, and MOIS leadership decapitation have temporarily suppressed coordinated high-end state APT operations from within Iran. However, external MOIS cells retain Stryker-class capability, the hacktivist swarm continues operations under the Islamic Resilience Cyber Axis framework, and the undersea cable threat introduces a new dimension of global disruption risk.
The April 6 Trump Hormuz deadline is the critical near-term trigger. If renewed energy infrastructure strikes occur, Iran cyber retaliation risk will sharply escalate, with Unit 42’s elevated wiper warning reflecting industry-wide anticipation of this pathway. MuddyWater’s confirmed presence in a U.S. bank and airport since February 2026 represents a potential pre-positioned destructive capability that could be activated in response to escalation. The long-term trajectory is concerning: multiple authoritative analyses assess that the war will produce an enduring increase in Iran’s cyber appetite and capability, following the North Korea model of cyber as strategic weapon.
PART 3: CROSS-DOMAIN ANALYSIS AND GEOPOLITICAL CONTEXT
3.1 Cross-Nation Convergence Patterns
Nation-state cyber operations in 2026 are no longer isolated, single-actor campaigns. The threat landscape has shifted toward a convergent model in which Russia, China, North Korea, and Iran share infrastructure, coordinate timing, and benefit from one another’s access—whether through formal state-to-state agreements or emergent proxy alignment. The Atlantic Council’s “Axis of Evasion” framework captures this dynamic: drones, navigation systems, and cyber capabilities flow between these actors in a network that amplifies each participant’s individual capability.
Russia-Iran Convergence
Russia-Iran convergence has escalated from hacktivist proxy support and intelligence sharing to confirmed direct military technology transfer. ISW confirmed on March 26 that Russia is shipping modified Shahed drone components (Garpiya-3), Geran-2 drones, and satellite imagery to Iran to assist strikes on U.S. and allied forces. EU Foreign Policy Chief Kaja Kallas stated publicly on March 26 that “Russia is helping Iran kill Americans” by providing intelligence. Iran originally transferred 600 disassembled Shahed-16 drones and components for 1,300 additional drones to Russia for the Ukraine campaign; by 2025, Russia assembled approximately 90% domestically. Russia has now reversed the flow, shipping improved variants back to Iran with modifications developed through Ukraine operational experience and Chinese specialist support. Russia denied Iran’s request for S-400 air defense systems. In cyberspace, pro-Russian hacktivist groups (NoName057(16), Cardinal, Russian Legion, Z-Pentest, and others) continue conducting operations in support of Iran’s position, providing psychological and disinformation cover.
Russia-DPRK Convergence
Russia-DPRK convergence operates primarily through a munitions-for-technology exchange framework. North Korea deployed 11,000+ troops to Russia’s Kursk front in 2024 for combat experience, and continues receiving financial aid, military technology, food, and energy in return for ammunition supplies. The ODNI 2026 ATA confirms this exchange has boosted DPRK revenue to its highest levels since before 2018 sanctions. In cyberspace, Gamaredon and Lazarus Group have been documented sharing C2 infrastructure, though the extent of deliberate coordination versus opportunistic overlap remains an open intelligence question.
China-Iran Convergence
China’s role in the Iran conflict ecosystem operates primarily through supply chain support rather than direct cyber collaboration. Iranian drones and missiles now incorporate Chinese BeiDou satellite navigation systems (access granted in 2021); since the war began, Iran uses BeiDou for decoy signals to confuse threat analysis and conceal military movements. U.S. Treasury sanctioned Chinese front companies supplying gyro navigation devices for Iranian UAVs in February and November 2025. Iranian shadow fleet vessels from China carry rocket fuel precursors. U.S. officials are monitoring signs that China may be weighing financial assistance and spare parts or missile-related components for Iran, though Beijing has avoided direct kinetic involvement partly due to energy security interests (China imports approximately 40% of its oil through the Hormuz corridor).
China-DPRK Convergence
China continues deepening influence over North Korea through infrastructure investment (new Yalu River Bridge construction) and strategic alignment (DPRK expressions of support for China’s Taiwan position). BeiDou satellite navigation access extends to DPRK military systems. No new reporting on direct cyber-specific China-DPRK cooperation emerged during this period, but the structural relationship provides enablement for DPRK operations through Chinese financial and technology channels.
Atlantic Council “Axis of Evasion” Framework
The Atlantic Council GeoEconomics Center (March 25) formalized the three-way convergence of Russian, Chinese, and Iranian supply chain cooperation. This framework recognizes that the four-nation convergence operates through layered mechanisms: formal state agreements (Russia-Iran drone transfers), commercial front companies (Chinese gyro navigation suppliers), shared navigation infrastructure (BeiDou), proxy hacktivist networks, and opportunistic criminal ecosystem overlap. The cumulative effect is a threat environment where disruption of any single actor’s capability may be partially compensated by partners’ contributions.
3.2 Geopolitical Triggers and Escalation Calendar
The next 30-90 days represent one of the most geopolitically loaded windows in recent years. Multiple potential escalation triggers cluster in April and May 2026, each carrying distinct cyber risk implications.
April 6 — Trump Hormuz Deadline (CRITICAL): Trump extended the pause on U.S. strikes against Iranian energy facilities by 10 days to April 6, requiring Iran to reopen the Strait of Hormuz or face destruction of power plants. Iran rejected a 15-point U.S. ceasefire proposal as “maximalist and unreasonable” and has set counter-conditions including sovereignty over Hormuz and reparations—non-starters for Washington. Brent crude approaching $120/barrel. If strikes proceed, Iranian cyber retaliation targeting U.S. energy infrastructure, financial systems, and allied targets should be anticipated within 24-72 hours.
May 14-15 — Trump-Xi Summit Confirmed (HIGH Espionage Risk): The summit creates a seven-week pre-summit espionage posture window. Chinese APT groups will intensify intelligence collection on tariff negotiations, AI chip access policy, and Taiwan arms sales cadence. China will avoid overt destructive operations that could derail the summit; espionage and pre-positioning are the expected operational modes.
Ukraine Spring Offensive (Ongoing, HIGH): Russia’s Spring 2026 offensive began March 17-21 with increased pressure on Ukraine’s Fortress Belt. ISW assesses Russia unlikely to seize the Fortress Belt in 2026. Peace talks are on “situational pause” with Polymarket probability of ceasefire by March 31 at 1%. Sustained wartime APT tempo against Ukraine and NATO allies will continue.
NATO Locked Shields Exercise (April 2026): The world’s largest live-fire cyber defense exercise follows the Partners’ Run completed March 26. Russian and pro-Russian actors may probe NATO participant networks during the exercise window.
Executive Order 14390 Deadlines: May 5 (60-day interagency review of TCO cyber frameworks) and July 4 (120-day full action plan due to President) create regulatory windows that may result in new sanctions designations and enforcement actions.
NATO Ankara Summit (July 7-8): Confirmed NATO summit in Turkey will draw elevated Russian APT and hacktivist targeting of allied communications and planning infrastructure.
3.4 Strategic Outlook and Forecast (Next 30-90 Days)
The near-term threat landscape is dominated by the April 6 Hormuz deadline. A failure to achieve diplomatic progress will likely result in renewed U.S. kinetic operations against Iranian energy infrastructure, triggering an immediate surge in Iranian cyber retaliation. MuddyWater’s confirmed pre-positioned access in U.S. networks, the Handala/MOIS capability for sub-24-hour reconstitution, and CyberAv3ngers’ reactivated OT scanning collectively represent the primary threat vectors for escalation-driven cyber attacks.
China’s threat posture will be defined by the pre-summit espionage window. Salt Typhoon and Volt Typhoon operations should be expected to continue and potentially intensify through mid-May. The BPFdoor disclosure suggests the intelligence community’s understanding of Chinese telecom penetration may be incomplete—additional disclosures of deeply embedded implants should be anticipated.
Russia’s wartime APT tempo will persist at current or elevated levels through the Spring offensive. The messaging app campaign represents an ongoing intelligence collection operation whose full scope is likely broader than currently disclosed. Hacktivist proxy operations on the Iran front will continue to expand as the conflict creates new targets of opportunity.
North Korea’s financial theft operations face no strategic constraints and will continue at or above current levels. The successful completion of Bybit laundering validates the DPRK financial pipeline, and new large-scale cryptocurrency platform compromises should be expected. The IT worker threat will continue to grow as long as remote work practices remain prevalent across the technology sector.
The single most dangerous scenario in the 30-day window is a simultaneous escalation on the Iran and Taiwan fronts, which would stretch U.S. cyber defense resources across multiple theaters and create opportunities for coordinated exploitation by all four nation-state adversaries.
PART 4: RECOMMENDED ACTIONS
4.1 Immediate Actions (24-72 Hours)
• Audit all Signal and WhatsApp linked devices across organizational accounts following the FBI/CISA PSA. Remove any unrecognized linked devices. Enable registration lock on Signal. Implement mandatory “Never Share Verification Codes” policy for all personnel with access to sensitive communications.
• Harden Microsoft Intune and Entra ID configurations per CISA’s March 18-19 endpoint management advisory. Enforce phishing-resistant MFA, implement multi-admin approval for device wipe/script execution actions, apply least-privilege access controls, and audit all Conditional Access policies.
• Deploy BPFdoor detection scanning on all Linux systems in telecom and critical infrastructure environments using the Rapid7-released scanning script. Conduct BPF filter enumeration, raw socket auditing, and process integrity validation on hardware management services.
• Block or monitor cloud storage services used for APT C2: filen.io, icedrive.net, and webhook.site. Evaluate blocking at the proxy/firewall level or implementing anomaly detection for unusual data transfers to these services from enterprise endpoints.
• Review financial sector exposure per FINRA cybersecurity alert on Iranian cyber actor targeting. Validate third-party vendor connections and supply chain security posture for financial services organizations.
4.2 Near-Term Actions (1-4 Weeks)
• Circulate DOJ/SDGA sentencing and Nisos laptop farm report to hiring teams, HR, and security awareness programs. Implement DPRK IT worker detection indicators including PiKVM, Tailscale, OConnect, IPMsg, and AI interview behavioral patterns. Screen all remote contractor laptop delivery addresses against identity documentation.
• Conduct tabletop exercise simulating Iranian escalation-driven wiper attack against organizational infrastructure, using the Stryker (Intune-based MDM abuse) and Handala (Telegram C2) TTPs as scenario basis. Include April 6 Hormuz deadline as trigger event.
• Validate backup and recovery procedures with specific focus on recovery from MDM management plane compromise scenarios. Ensure backup infrastructure is isolated from identity and device management systems that could be weaponized for bulk destruction.
• Patch all Hikvision and Dahua camera systems per the CVEs being actively exploited by CyberAv3ngers (CVE-2017-7921, CVE-2021-36260, CVE-2023-6895, CVE-2025-34067, CVE-2021-33044). Segment IoT/camera networks from operational technology environments.
• Monitor npm and PyPI package repositories for Famous Chollima StegaBin variants. Implement software composition analysis scanning and restrict installation of unvetted packages in development environments.
4.3 Ongoing/Strategic
• Implement defense-in-depth for telecom environments assuming kernel-level implants may already be present. This includes network behavior anomaly detection, SCTP traffic monitoring, and periodic raw socket audits—not just perimeter-focused controls.
• Review DNI ATA 2026 with organizational leadership as the authoritative IC endorsement of CRITICAL threat levels across all four nation-state adversaries. Use as basis for cyber budget justification, staffing requests, and board-level risk communication.
• Establish continuous intelligence monitoring for April 6 Hormuz deadline developments, May 14-15 Trump-Xi Summit pre-positioning indicators, and any change in Iran’s internet connectivity above the current ~1% threshold (which would be the strongest indicator of impending high-end APT operation resumption).
• Engage with sector ISACs on cross-sector threat intelligence sharing, particularly for energy, financial services, healthcare, and telecommunications sectors that face overlapping targeting from multiple nation-state adversaries.
5.5 Distribution and Handling
This document is classified UNCLASSIFIED // OSINT and is approved for distribution to strategic decision-makers and cybersecurity leadership within the intended recipient organization. All source material is derived from publicly available open-source intelligence.
This briefing does not contain classified information and may be shared with external partners at the recipient’s discretion. Recipients are encouraged to share relevant indicators of compromise and defensive recommendations with their sector Information Sharing and Analysis Centers (ISACs) and trusted partners.
Questions, corrections, or requests for additional analysis should be directed to the producing analyst.
Prepared: March 27, 2026
Next Scheduled Update: April 3, 2026